… updated on Sunday, April 13, 2025 09:05 +0200
Network Migration with BGP Local-AS Feature
The Cisco IOS BGP Local-AS feature allows a BGP-speaking router to impersonate an autonomous system different from the one configured with the router bgp global configuration command. Its primary use facilitated seamless AS mergers; later additions made it applicable to AS renumbering scenarios. In the meantime, most other network operating systems implemented equivalent features (netlab can configure local AS functionality on over a dozen platforms)
The BGP Local-AS feature is usually configured with the neighbor IP-address local-as AS-number router configuration command. Subsequent IOS releases added the no-prepend keyword to clean up the AS path, as well as replace-as and dual-as keywords to support AS renumbering.
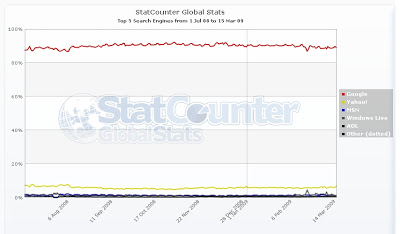
Off-topic: Search engine wars are over
As you can see, Google has approximately 90% market share, Yahoo (the second place) has less than 10%, the others are clearly irrelevant.
Recovering from expired one-time username
A reader sent me an interesting question:
Do you have any advice for resetting/logging into a router (2821) where the one time user of cisco:cisco has already been used?
I couldn't offer any better advice than performing the regular password recovery procedure. Is there another solution?
This article is part of You've asked for it series.
… updated on Tuesday, December 29, 2020 07:37 UTC
EBGP Load Balancing with a Multihop EBGP Session
Multihop EBGP sessions are the traditional way to implement EBGP load balancing on parallel links. EBGP session is established between loopback interfaces of adjacent routers (see the next diagram; initial router configurations are included at the bottom of the article) and static routes (or an extra instance of a dynamic routing protocol) are used to achieve connectivity between loopback interfaces (BGP next-hops). The load balancing is an automatic result of the recursive route lookup of BGP next hops.
Fat finger follow-up: use the key labels
Karsten Iwen made an interesting comment to my “Don't let a lab rat anywhere near a production box” post: you should avoid the SSH/VPN key generation mistakes by using key labels. He also wrote a post explaining the concept but since it’s in German, let me rephrase it in English.
Cisco IOS release 12.2(8)T added the label parameter to the crypto key generate rsa command. You can use this parameter to assign a label to your VPN key, for example
Build a VPN Across Your IP Network with Multi-VRF Feature
One of our customers had to provide end-to-end IP transport across their enterprise network for an outsourced video surveillance solution. We implemented a true VPN solution for them (the hosts in the enterprise network cannot access the surveillance equipment and vice versa) using the Multi-VRF feature available in all recent Cisco IOS releases.
Are you willing to talk about SP infrastructure optimization?
Don't let a lab rat anywhere near a production box
I tried to do a few simple NETCONF tests yesterday (I wanted to see how the router's configuration looks like when it's encoded in XML). I didn't want to start a lab for such a simple task and decided to use my home router. SSH was the only reasonable transport (you can't run BEEP with standard Linux tools), but it was not working on the router.
Off-topic: Marketing 2.0
 It's almost guaranteed to be a winning combination in a Bullshit Bingo.
It's almost guaranteed to be a winning combination in a Bullshit Bingo.
Generating syslog messages from Tcl
If you use Tcl to write Embedded Event Manager policies, you could use the action_syslog command to generate syslog messages. In all other Tcl-based environments (including tclsh), this API is not available, but you could use the syslog: file system to generate debugging messages.