Blog Posts in January 2022
… updated on Monday, January 31, 2022 19:26 UTC
Sample Lab: SR-MPLS on Junos and SR Linux
Last week I published a link to Pete Crocker’s RSVP-TE lab, but there’s more: he created another lab using the same topology that uses SR-MPLS with IS-IS to get the job done.
Jeroen Van Bemmel did something similar for SR Linux: his lab topology has fewer devices (plus SR Linux runs in containers), so it’s easily deployable on machines without humongous amount of memory.
Worth Reading: The Network Does Too Much
Tom Hollingsworth published a more eloquent version of what I’ve been saying for ages:
- Complexity belongs to the end nodes;
- Network should provide end-to-end packet transport, not a fix for every stupidity someone managed to push down the stack;
- There’s nothing wrong with being a well-performing utility instead of pretending your stuff is working on unicorn farts and fairy dust.
Obviously it’s totally against the vested interest of any networking vendor out there to admit it.
Worth Exploring: Christoph Jaggi's New Web Site
Christoph Jaggi, the author of Ethernet Encryption webinar and ethernet encryptor market overviews launched a new site in which he collected tons material he created in the past – the network security and news and articles sections are definitely worth exploring.
Video: Kubernetes Architecture
Yesterday I mentioned the giant glob of complexity called Kubernetes (see also more nuanced take on the topic). If you want to slowly unravel it, Kubernetes Architecture video from the excellent Kubernetes Networking Deep Dive webinar by Stuart Charlton is a pretty good starting point.
MTU Settings in Virtual Network Devices
When I finally1 managed to get SR Linux running with netlab, I wanted to test how it interacts with Cumulus VX and FRR in an OSPF+BGP lab… and failed. Jeroen Van Bemmel quickly identified the culprit: MTU. Yeah, it’s always the MTU (or DNS, or BGP).
I never experienced a similar problem, so of course I had to identify the root cause:
Three Dimensions of BGP Address Family Nerd Knobs
Got into an interesting BGP discussion a few days ago, resulting in a wild chase through recent SRv6 and BGP drafts and RFCs. You might find the results mildly interesting ;)
BGP has three dimensions of address family configurability:
- Transport sessions. Most vendors implement BGP over TCP over IPv4 and IPv6. I’m sure there’s someone out there running BGP over CLNS1, and there are already drafts proposing running BGP over QUIC2.
- Address families enabled on individual transport sessions, more precisely a combination of Address Family Identifier (AFI) and Subsequent Address Family Identifier.
- Next hops address family for enabled address families.
More: Hardware Differences between Routers and Switches
Aaron Glenn sent me his thoughts on hardware differences between routers and switches based on the last paragraph of Dmytro Shypovalov’s views on the topic
To conclude, what is the difference between routers and switches in my opinion? I have absolutely no idea.
Sample Lab: RSVP TE on Junos
It’s amazing how creative networking engineers become once they have the basic tools to get the job done a bit quicker. Last week Pete Crocker published the largest topology I’ve seen built with netlab so far: a 13-router lab running RSVP TE to transport IP traffic between external autonomous systems1.
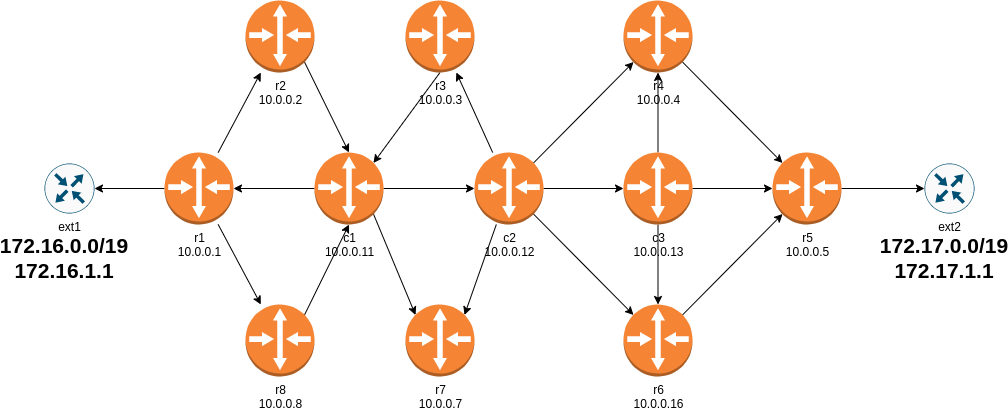
Lab topology
Video: Machine Learning Techniques
After Javier Antich walked us through the AI/ML hype and described the basics of machine learning it was time for a more thorough look at:
- Machine learning techniques, including unsupervised learning (clustering and anomaly detection), supervised learning (regression, classification and generation) and reinforced learning
- Machine learning implementations, including neural networks, deep neural networks and convolutional neural networks.
Introducing netlab Plugins
Remember the BGP anycast lab I described in December 2021? In that blog post I briefly mentioned a problem of extraneous IBGP sessions and promised to address it at a later date. Let’s see how we can fix that with a netlab plugin.
We always knew that it’s impossible to implement every nerd knob someone would like to have when building their labs, and extending the tool with Python plugins seemed like the only sane way to go. We added custom plugins to netlab in late 2021, but I didn’t want to write about them because we had to optimize the internal data structures first.
Layer-3 Carrier Ethernet
One of ipSpace.net subscribers asked for my opinion about Adaptive IP, a concept promoted by one of the optical connectivity vendors. As he put it:
My interest in Carrier Ethernet moving up to Layer 3 is to see if it would be something to account for in the future.
A quick search resulted in a marketecture using Segment Routing (of course) and an SDN controller (what else could one be using today) using Path Computation Element Protocol (PCEP) to program the network devices… and then I hit a regwall. They wanted to collect my personal details to grace me with their whitepaper, and I couldn’t find even a link to the product documentation.
Running IS-IS over Unnumbered Ethernet Interfaces
Last time we figured out that we cannot run OSPF over unnumbered interfaces that are not point-to-point links because OSPF makes assumptions about interface IP addresses. IS-IS makes no such assumptions; IPv4 and IPv6 prefixes are just a bunch of TLVs exchanged between routers over a dedicated layer-3 protocol with ridiculously long network addresses.
Could we thus build a totally unnumbered IP network with IS-IS even when the network contains multi-access segments? It depends:
Video: Local Area Network Addressing
In the Local Area Network Addressing video (part of How Networks Really Work webinar) I covered numerous obscure LAN addressing details including:
- There’s no layer-2 address in Fibre Channel frames (because FC is routing not bridging);
- Why is the multicast bit the lowest bit (0x01) in the first byte on Ethernet but the highest bit (0x80) on Token Ring or FDDI;
- How some NIC manufacturers never got the memo on what OUI really means.
Feedback: Recursive BGP Next Hop Resolution
The Recursive BGP Next Hops: an RFC 4271 Quirk blog post generated tons of feedback (thanks a million to everyone writing a comment on my blog or LinkedIn).
Starting with Robert Razsuk who managed to track down the original email that triggered the (maybe dubious) text in RFC 4271:
The text in section 5.1.3 was not really targeting to prohibit load balancing. Keep in mind that it is FIB layer which constructs actual forwarding paths.
The text has been suggested by Tom Petch in discussion about BGP advertising valid paths or even paths it actually installs in the RIB/FIB. The entire section 5.1.3 is about rules when advertising paths by BGP.
Just Out: netsim-tools Release 1.1
New Year break was probably my busiest time (programming-wise) in years. Jeroen van Bemmel continued generating great ideas (and writing code and device configuration templates), and I found myself saying, “why not, let’s do the right thing!” more often than I expected. In parallel, Stefano Sasso fixed configuration templates for Junos, Mikrotik Router OS, and VyOS, and we were good to go.
To give you an idea of how fast we were moving: issue #84 was created on December 22nd, Sunday’s pull request that pushed release 1.1 into the master branch was #135 (GitHub numbers everything you do sequentially).
… updated on Tuesday, August 22, 2023 15:17 UTC
Running OSPF over Unnumbered Ethernet Interfaces
Remember the unnumbered IP interfaces saga? Let’s conclude with the final challenge: can we run link-state routing protocols (OSPF or IS-IS) over unnumbered interfaces?
Quick answer: Sure, just use IPv6.
Cheater! IPv6 doesn’t count. There are no unnumbered interfaces in IPv6 – every interface has at least a link-local address (LLA). Even more, routing protocols are designed to run over LLA addresses, including some EBGP implementations, allowing you to build an LLA-only network (see RFC 7404 for details).
OK, what about IPv4?
TL&DR: It works, but…
Worth Reading: Free Software Is a Gift
I’m positive that this pointer to The Gift of It’s Your Problem Now by Avery Pennarun will generate similar comments to the blockchain one: “he’s an idiot, and you’re an idiot for wasting my time posting this”.
That might be true, but in that case he’s my kind of idiot, and you shouldn’t complain about a gift anyway – there are tons of high-quality lolcats videos waiting for you instead.
Video: Cloud Services Hierarchy
Remember the Cloud Models, Layers and Responsibilities video by Matthias Luft? He continued his introduction of cloud services with Cloud Services Hierarchy, explained the differences between infrastructure, platform, function and software as a service, and concluded with a there’s no free lunch message.
Feedback: Cisco ACI Deep Dive
In 2021, we completed one of the longest ipSpace.net webinars: Cisco ACI Deep Dive (almost 13 hours of content1). One of the participants found it extremely useful:
I really like the technical detail of the webinar and the way it is composed. Mario also does a good job in explaining all the complexity in a clear way without oversimplifying. All the sessions help to build up an understanding on the inner workings of the ACI solution, because they deliver technical details in depth piece by piece.
I also liked his take on the value of this webinar:
I’m always amazed on how much other (offical) training vendors under deliver in their courses that cost thousands of dollars, compared to the real expert level stuff you’ve got here.
Hope you’ll like the webinar as much as he did – you can get it with Standard or Expert ipSpace.net Subscription.
Recursive BGP Next Hops: an RFC 4271 Quirk
All BGP implementations I’ve seen so far use recursive next hop lookup:
- The next hop in the IP routing table is the BGP next hop advertised in the incoming update
- That next hop is resolved into the actual next hop using one or more recursive lookups into the IP routing table.
Furthermore, all BGP implementations I’ve seen used multiple recursive next hops (if available) to implement load balancing toward the BGP next hop – that’s how we made EBGP load balancing work in Stone Age of networking.
Microsegmentation Terminology
While I liked reading the Where to Stick the Firewall blog post by Peter Welcher, it bothered me a bit that he used microsegmentation to mean security groups.
I know that microsegmentation became approximately as well-defined as cloud or SDN1, but let’s aim our shiny lance 2 at the nearest windmill and gallop away…
netsim-tools: New in December 2021
Tons of new things were added to netsim-tools in December 2021:
- Pete Crocker contributed support for Fortinet devices. You can configure IPv4, IPv6 and OSPF. More details…
- Jeroen van Bemmel contributed support for Nokia SR Linux and SR OS (including initial device configuration, OSPF, ISIS, BGP, and SR-MPLS).
- I added Vagrant box names for IOSv, CSR and vSRX on VirtualBox. You still have to build the boxes, but at least you won’t have to change the default settings.
