The Many Paths to SDN
I did a major overhaul of my RIPE 65 SDN presentation prior to MENOG 12 meeting, including a more comprehensive overview of SDN-related technologies sorted by the networking device plane they operate on.
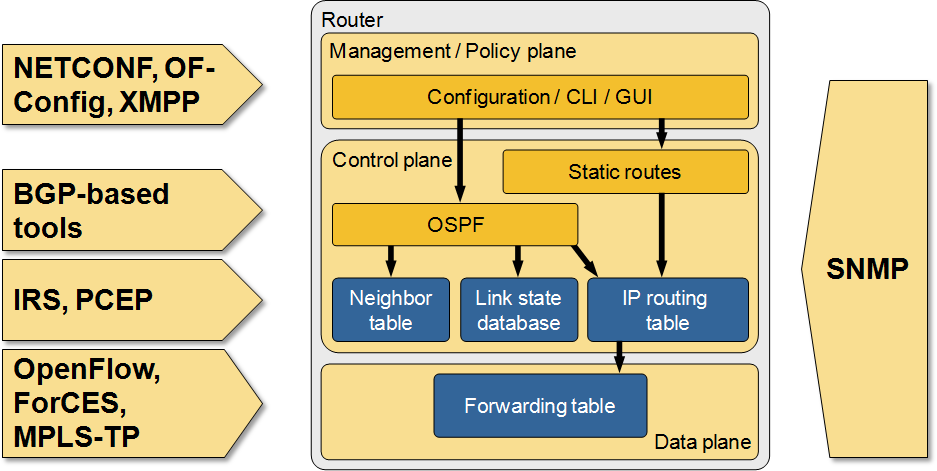
Many paths to SDN
The Impact of Changed NHRP Behavior in DMVPN Networks
Two years ago I wrote the another Fermatish post: I described how NHRP behavior changed in DMVPN networks using NAT and claimed that it might be a huge problem, without ever explaining what the problem is.
Fabrice quickly identified the problem, but it seems the description was not explicit enough as I’m still getting queries about that post, so here’s a step-by-step description of what’s going on.
VLANs are the wrong abstraction for virtual networking
Are you old enough to remember the days when operating systems had no file system? Fortunately I never had to deal with storing files on one of those (I was using punch cards), but miraculously you can still find the JCL DLBL/EXTENT documentation online.
On the other hand, you probably remember the days when a SCSI LUN actually referred to a physical disk connected to a computer, not an extensible virtual entity created through point-and-click exercise on a storage array.
You might wonder what the ancient history has to do with virtual networking. Don’t worry we’re getting there in a second ;)
IPv6 Source Address Validation Improvement
We learned how to deal with ARP and IP spoofing in IPv4 networks. Every decent switch has DHCP snooping, ARP protection, and IP source guard (or whatever the features are called), but validating source IPv6 addresses in security-conscious environments or public multi-access networks remains a major headache.
It would be pretty easy to solve the problem with a central controller, but IETF decided to go another way and developed yet another framework: Source Address Validation Improvements (SAVI). For more information, watch the following video from IPv6 Security webinar in which Eric Vyncke describes the intricacies of SAVI in great details.
Where Is my VLAN Provisioning Application?
Yesterday I wrote that it’s pretty easy to develop a VLAN provisioning application (integrating it with vCenter or System Center earns you bonus points, but even that’s not too hard), so based on the frequent “I hate using CLI to provision VLANs” rants you might wonder where all the startups developing those applications are. Simple answer: there’s no reasonably-sized market. How would I know that? We’ve been there.
What Did You Do to Get Rid of Manual VLAN Provisioning?
I love(d) listening to the Packet Pushers podcast and came to expect the following rant in every SDN-focused episode: “I’m sick and tired of using CLI to manually provision VLANs”. Sure, we’re all in the same boat, but did you ever do something to get rid of that problem?
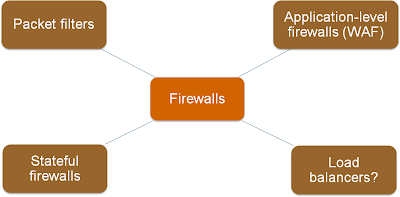
The Spectrum of Firewall Statefulness
One of the first slides I created for the Virtual Firewalls webinar explained various categories of traffic filters, from stateless (and fast) packet filters to application-level firewalls.
As always, the real life is not black-and-white; I found a whole spectrum of products in the wild.
Control-plane policing in OpenFlow networks
The Controller-Based Packet Forwarding in OpenFlow Networks post generated the obvious question: “does that mean we need some kind of Control-Plane Protection (CoPP) in OpenFlow controller?” Of course it does, but things aren’t as simple as that.
ProgrammableFlow Configuration Interfaces
Like every recently designed fabric configuration/management platform, NEC ProgrammableFlow controller supports numerous configuration interfaces, including CLI, GUI, web-based configuration, REST API and OpenStack plugin. For more details, watch this part of the ProgrammableFlow Technical Deep Dive webinar.
Does dedicated iSCSI infrastructure make sense?
Chris Marget recently asked a really interesting question:
I’ve encountered an environment where the iSCSI networks are built just like FC networks: Multipathing software in use on servers and storage, switches dedicated to “SAN A” and “SAN B” VLANs, and full isolation of paths (redundant paths) between server and storage. I understand creating a dedicated iSCSI VLAN, but why would you need two? Isn’t the whole thing running on top of TCP? Am I missing something?
Well, it actually makes sense in some mission-critical environments.