BGP Labs: Use BGP Communities in a Routing Policy
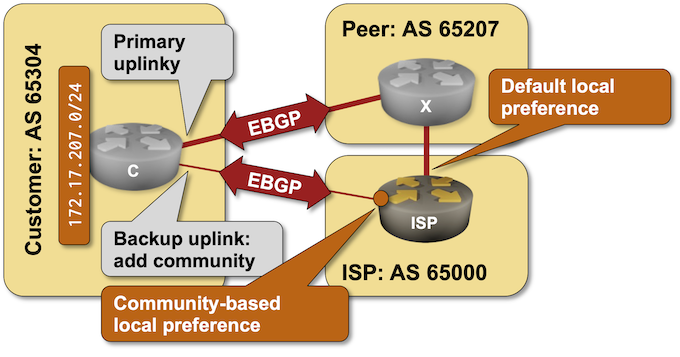
A previous BGP lab focused on the customer side of BGP communities: adding them to BGP updates to influence upstream ISP behavior. Today’s lab focuses on the ISP side of the equation: using BGP communities in a routing policy to implement RFC 1998-style behavior.
Interviewing a Network Engineer Using a Single Scenario
I always said that the Trivia Pursuit certification tests (or job interviews) are nonsense and that one should focus on fundamentals.
In a recent blog post, Daniel Dib described a fantastic scenario: using a simple “why can’t I connect to a web site” question, explore everything from ARP/ND to DNS and TLS.
Obviously, you’ll never see anything that sane in a certification test. An interactive interview doesn’t scale (beyond CCDE), and using humans (and common sense judgment) creates potential legal liabilities (there were rumors that had been one of the reasons a talk with a proctor who could flunk you was dropped from the CCIE test).
Response: Vendor Network Automation Tools
Drew Conry-Murray published a excellent summary of his takeaways from the AutoCon0 event, including this one:
Most companies want vendor-supported tools that will actually help them be more efficient, reduce human error, and increase the velocity at which the network team can support new apps and services.
Yeah, that’s nothing new. Most Service Providers wanted vendors to add tons of nerd knobs to their products to adapt them to existing network designs. Obviously, it must be done for free because a vast purchase order1 is dangling in the air. We’ve seen how well that worked, yet learned nothing from that experience.
Worth Reading: Network CI and Open Source
Did you find the Network Automation with GitHub Actions blog post interesting? Here are some more GitHub Self-Hosted Runner goodies from Julio Perez: Network CI and Open Source – Welcome to the World of Tomorrow. Enjoy!
Worth Exploring: SRv6 Test Topologies
Want to explore SRv6? Cisco engineers put together a repository containing scripts and configs for building SRv6 test topologies. It works with Containerlab and FRR (unless you want to beg a Cisco account team for a Cisco 8000 image or make a sandwich while the IOS XRd image is booting).
Want to use netlab? Jeroen van Bemmel implemented baseline SRv6 support for Nokia SR OS.
Video: netlab IP Address Management (IPAM)
Did you know that netlab includes full-blown IP address management? You can define address pools (or use predefined ones) and get IPv4 and IPv6 prefixes from those pools assigned to links, interfaces, and loopbacks. You can also assign static prefixes to links, use static IP addresses, interface addresses as an offset within the link subnet, or use unnumbered interfaces.
For an overview of netlab IPAM, watch the netlab address management video (part of the Network Automation Tools webinar), for more details read the netlab addressing tutorial.
AMS-IX Outage: Layer-2 Strikes Again
On November 22nd, 2023, AMS-IX, one of the largest Internet exchanges in Europe, experienced a significant performance drop lasting more than four hours. While its peak performance is around 10 Tbps, it dropped to about 2.1 Tbps during the outage.
AMS-IX published a very sanitized and diplomatic post-mortem incident summary in which they explained the outage was caused by LACP leakage. That phrase should be a red flag, but let’s dig deeper into the details.
BGP Labs: Use BGP Route Reflectors
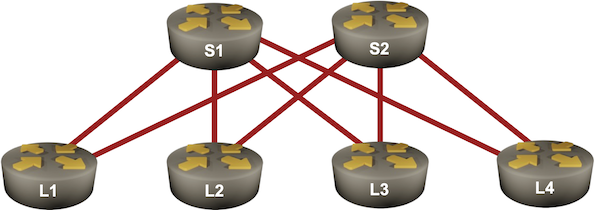
In the previous BGP labs, we built a network with two adjacent BGP routers and a larger transit network using IBGP. Now let’s make our transit network scalable with BGP route reflectors, this time using a slightly larger network:
netlab 1.7.0: Lab Validation, Fabrics, BGP Nerd Knobs
It’s been a while since the last netlab release. Most of that time was spent refactoring stuff that you don’t care about, but you might like these features:
- You can run automated lab validation tests with the netlab validate command. I will explain how I use that in BGP labs in a few days.
- If you want to build large leaf-and-spine topologies, you’ll love the fabric plugin.
- The bgp.domain plugin allows you to create topologies with multiple sites using the same BGP AS number.
- The bgp.policy plugin got AS-path prepending.
- bgp.originate plugin can be used to originate BGP IPv4 and IPv6 prefixes.
As always, we also improved the platform support:
The BGP Origin Attribute
Kristijan Taskovski asked an interesting question related to my BGP AS-prepending lab:
I’ve never personally done this on the net but….wouldn’t the BGP origin code also work with moving one’s ingress traffic similarly to AS PATH?
TL&DR: Sort of, but not exactly. Also, just because you can climb up ropes using shoelaces instead of jumars doesn’t mean you should.
Let’s deal with the moving traffic bit first.
