Packet Forwarding in Amazon VPC
Packet forwarding behavior of VMware NSX and Hyper-V Network Virtualization is well documented; no such documentation exists for Amazon VPC. However, even though Amazon uses a proprietary solution (heavily modified Xen hypervisor with homemade virtual switch), it’s pretty easy to figure out the basics from the observed network behavior and extensive user documentation.
Chiradeep Vittal ran a number of tests between virtual machines in an Amazon VPC network and shared the results in a blog post and extensive comments on one of my posts. Here’s a short summary:
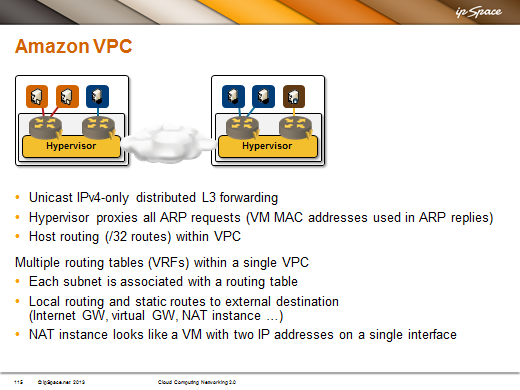
- Virtual switches in Amazon VPC perform layer-3-only unicast IPv4 forwarding (similar to recent Hyper-V Network Virtualization behavior). All non-IPv4 traffic and multicast/broadcast IPv4 traffic is dropped.
- Layer-3 forwarding in the hypervisor virtual switch does not decrement TTL – it’s like all virtual machines reside in the same subnet;
- Hypervisor proxies all ARP requests and replies with the expected MAC addresses of target VMs or first-hop gateway (early implementations of Amazon VPC used the same destination MAC address in all ARP replies);
- Virtual switch implements limited router-like functionality. For example, the default gateway IP address replies to pings, but a VM cannot ping the default gateway of another subnet.
Seems like a run-of-the-mill virtual networking implementation, but wait – that’s not all. The beauty of Amazon VPC forwarding model is the multi-VRF approach: you can create multiple routing tables in your VPC and assign one of them to each subnet.
You could, for example, use the default route toward the Internet for web server subnet, default route toward your data center for database server subnet, and no default routing (local connectivity only) for your application server subnet. Pretty cool stuff if you’re an MPLS/VPN geek used to schizophrenic routing tables, and quite a tough nut to crack for people who want to migrate their existing layer-2 networks into the cloud. Massimo Re Ferre made a perfect summary: everyone else is virtualizing the network, Amazon VPC is abstracting it.
More information
I’m describing virtual networking models of Cisco’s and VMware’s VXLAN, VMware NSX, vCloud Director, Hyper-V Network Virtualization, Juniper Contrail and Amazon VPC in Cloud Computing Networking webinar.
Overlay Virtual Networking webinar goes deeper into the commercially available architectures from numerous vendors, including Cisco, VMware, Microsoft, IBM, and Midokura.

http://www.youtube.com/watch?v=Zd5hsL-JNY4
Very fun post. Stick it to the man.
I just wanted to thank you for the insane amount of posts you've put out this year. Not one of them was a waste of time. It was hard for me to keep up and I hope I did not miss too many. I do not know how you do it!
Will