Blog Posts in July 2013
More Private AS Numbers
Have you ever tried to implement a large-scale DMVPN or MPLS/VPN network using BGP as the routing protocol? If you tried to stitch more than ~1000 sites together you’re well aware of all the pain caused by a small range of private AS numbers defined in RFC 1930. We can kludge our way around the limitation by reusing the same AS number on multiple sites (and using allowas-in when we need full routing information on every site), but such a design clearly sucks.
Cloud-as-an-Appliance Design
The original idea behind cloud-as-an-appliance design came from Brad Hedlund’s blog post in which he described how he’d build a greenfield Hadoop or private cloud cluster with servers connected to a Clos fabric. Throw virtual appliances into the mix and you get an extremely simple and versatile architecture:
Unreadable IPv6 Addresses Might Be Good For Us in the Long Run
One of the first arguments used by networking engineers living in IPv6 denial and trying to justify their stance is “IPv6 addresses are unreadable. We will never migrate to IPv6; it’s much easier to deal with IPv4 addresses.”
That’s absolutely true. If you use RFC 1918 addresses in a small(ish) network, the first two octets don’t change, and it’s easy to remember the remaining two numbers … but the unreadable IPv6 addresses just might change the way we approach network configuration and monitoring.
Published on , commented on July 9, 2022
Where’s the Revolutionary Networking Innovation?
In his recent blog post Joe Onisick wrote “What network virtualization doesn’t provide, in any form, is a change to the model we use to deploy networks and support applications. [...] All of the same broken or misused methodologies are carried forward. [...] Faithful replication of today’s networking challenges as virtual machines with encapsulation tunnels doesn’t move the bar for deploying applications.”
Unicast-Only VXLAN Finally Shipping
The long-promised unicast-only VXLAN has finally shipped with the Nexus 1000V release 4.2(1)SV2(2.1) (there must be some logic behind those numbers, but they all look like madness to me). The new Nexus 1000V release brings two significant VXLAN enhancements: unicast-only mode and MAC distribution mode.
Downloadable Recording of Enterasys Data Center Interconnect Solutions Webinar
The recording of recent Enterasys Robust Data Center Solutions is available on ipSpace.net demo web site.
You can watch (or download) the following videos:
First-Hop IPv6 Security Features in Cisco IOS
I wanted to figure out how to use IPv6 DAD proxy in PVLAN environments during my seaside vacations, and as I had no regular Internet access decided to download the whole set of IPv6 configuration guides while enjoying the morning cup of coffee in an Internet café. Opening the IPv6 First-Hop Security Configuration Guide was one of the most pleasant (professional) surprises I had recently.
One word summary: Awesome.
Doodling on a Napkin
Two more books you must read during your summer vacation: The Back of the Napkin and Unfolding the Napkin ... and here are a few drawing tools that work for me.
If you’re anything like me, your first results will be disastrous. Keep practicing; I’m able to draw understandable (if not pretty) diagrams by now (and I’m still trying to stay away from Pictionary).
Smart Fabrics Versus Overlay Virtual Networks
With the recent plethora of overlay networking startups and Cisco Live Dynamic Fabric Architecture announcements it’s time to revisit a blog post I wrote a bit more than a year ago, comparing virtual networks and voice technologies.
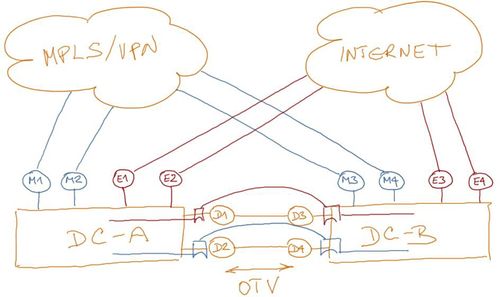
They say a picture is worth a thousand words – here are a few slides from my Interop 2013 Overlay Virtual Networking Explained presentation.
ProgrammableFlow Typical Use Cases
The last part of the ProgrammableFlow webinar described typical use cases including Cloud-as-an-Appliance, traffic steering (used by appliances like Radware DefenseFlow) and hypervisor switching with PF1000. Predictably, the use cases were followed by a lengthy Q&A session.
… updated on Thursday, April 23, 2020 05:30 UTC
The Tools That I Use (Drawings)
Continuing from the previous Tools That I Use post, here’s what I’m using to generate the hand drawings in blog posts and case studies.
Wacom Cintiq with SketchBook Pro has been indispensable for high-resolution drawings I used in case studies. I’ve tried to import router symbols in SketchBook Pro and make them look like they would be hand-drawn, but my illustrating skills are almost non-existent.
Typical SketchBook Pro drawing
Cloudbursting, the Wally Way
Priceless! (source: Dilbert.com)
… updated on Thursday, November 19, 2020 12:17 UTC
iSCSI with PFC?
Nicolas Vermandé sent me a really interesting question: “I've been looking for answers to a simple question that even different people at Cisco don't seem to agree on: Is it a good idea to class IP traffic (iSCSI or NFS over TCP) in pause no-drop class? What is the impact of having both pauses and TCP sliding windows at the same time?”
IPv6 Address Assignment and Tracking
One of the significant challenges of IPv6 is the host address assignment and tracking (for logging/auditing reasons), more so if you use SLAAC or (even worse) SLAAC privacy extensions. Not surprisingly, Eric Vyncke and I spent significant time addressing this topic in the IPv6 Security webinar.
Published on , commented on July 9, 2022
Fallacies of GUI
I love Greg Ferro’s characterization of CLI:
We need to realise that the CLI is a “power tools” for specialist tradespeople and not a “knife and fork” for everyday use.
However, you do know that most devices’ GUI offers nothing more than what CLI does, don’t you? Where’s the catch?
Summer seems to have arrived
The current weather around Central Europe doesn’t exactly support this conclusion, but I do get many more “I’m on vacation” responses than usual, so it’s time to reduce the blogging frequency to keep your RSS reader from overloading (you did switch from Google Reader to something like Feedly, didn’t you?).
However, if you’re looking for some really heavy reading, do pick up The Hidden Reality and explore various multiverse proposals. There’s also a beach-friendly version of multiverse discussion: The Long Earth by the one-and-only Terry Pratchett.

