You MUST Take Control of IPv6 in Your Network
I’m positive most of you are way too busy dealing with operational issues to start thinking about IPv6 deployment (particularly if you’re working in the enterprise world; European service providers using the same “strategy” just got a rude wake-up call). Bad idea – if you ignore IPv6, it will eventually blow up in your face. Here’s how:
I was writing about the fun you could have enabling IPv6 on an unprotected wireless network (or campus LAN) a while ago. The same thing can happen in your data center. Most recently-released operating systems have IPv6 enabled by default; the moment someone accidentally (or on purpose) starts sending RA messages, all the servers on the same LAN get auto-configured IPv6 addresses.
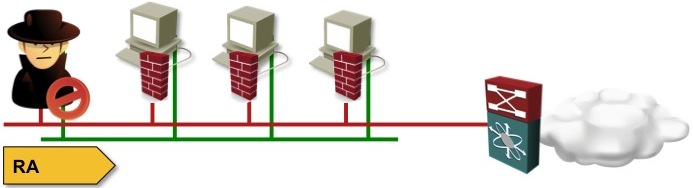
An intruder happily enjoying a free ride on a network that tries to ignore the realities of IPv6
What happens next depends on your firewall strategy and the operating system you’re using:
- If you’re not using host-based firewalls, you have a problem anyway (but it’s not getting any worse due to IPv6). The moment one of the servers gets pwned, all other servers become an easy target;
- If you’re running Linux, you’re probably using iptables. IPv6 is using ip6tables (you did configure them, didn’t you?). Windows is better – its firewall works on IPv4 and IPv6.
- If you’re protecting your servers with hypervisor-based firewalls like vShield App or Virtual Security Gateway, your VMs might become exposed, as these firewalls don’t support IPv6… but then maybe they throw away unknown protocols. Feedback welcome!
So are you safe if you’re running Windows on your servers? Actually not, this was just the appetizer. When I was asking Mrs. Y, the host of the excellent Healthy Paranoia security podcast whether my ramblings make sense, she immediately got creative:
But I could see far worse scenarios. I could use a dual stack server environment to exploit trust between hosts, MITM attacks, DNS cache poisoning. I could set up a DHCPv6 stateless server, just setting bogus RDNS options. Or, some hosts will actually get their RDNS options from SLAAC, because they run an RDNSS.
Additionally, are you blocking transition mechanisms at the border? 6to4 and Teredo? I can always use those as exfiltration mechanisms from your servers too. I would have IPS on data center networks looking for IPv6 traffic, even if you aren't officially supporting the protocol. I'm betting there's plenty there.
In any case, you have to take control. You can enable RA guard (you did buy switches with IPv6 support and RA guard, didn’t you?), but even that could by bypassed. You could disable IPv6 on all servers, or filter IPv6 ethertype on layer-2 switches. Regardless of what you decide to do, do not ignore IPv6. It will not go away anytime soon.
Resources to get you started
- I wrote a lot about IPv6.
- Cisco has IPv6 design guides for campus and branch networks.
- Juniper has Junos Day One books: Exploring IPv6 and Advanced IPv6.
- Cisco Press published several excellent IPv6 books, including IPv6 Security and IPv6 for Enterprise Networks.
- I’ve created several IPv6 webinars, including the IPv6 security webinar. You can get access to all of them with the yearly subscription.

You already mentioned the Healthy Paranoia security podcast, which is great. The latest, IPv6 Security Smackdown, has some great tools and resources in the shownotes. The NIST SP800-119 guidelines needs a special mention.
To get started with implementing IPv6 in your network and get to know IPv6 in general I can endorse this document by the Dutch SURF-net...
http://www.surfnet.nl/Documents/handleiding_201012_IPv6_nummerplan_EN.pdf
Per the Microsoft IPv6 FAQ (http://technet.microsoft.com/en-us/network/cc987595.aspx), “From Microsoft's perspective, IPv6 is a mandatory part of the Windows operating system and it is enabled and included in standard Windows service and application testing during the operating system development process. Because Windows was designed specifically with IPv6 present, Microsoft does not perform any testing to determine the effects of disabling IPv6. If IPv6 is disabled on Windows 7, Windows Vista, Windows Server 2008 R2, or Windows Server 2008, or later versions, some components will not function. Moreover, applications that you might not think are using IPv6—such as Remote Assistance, HomeGroup, DirectAccess, and Windows Mail—could be.”
Vanilla install of Exchange with services dispatched on a number of servers.
By default and without any IPv6 configuration, the incoming/outgoing mail path contains an IPv6 hop between two of the nodes that share a common subnet, using fe80:: local IPs.
You might not do IPv6, but you're advertising differently in your mail headers....