Blog Posts in January 2010
Bug in EEM SNMP event detector
Jared Valentine found an interesting bug in the EEM’s SNMP event detector: if you’re triggering your EEM applet when the increment of an SNMP variable exceeds the threshold, you cannot re-arm the applet; the exit-type increment does not work. He fixed the problem with a somewhat more convoluted approach:
- The first EEM applet reads the SNMP variable, waits a second, does a second read and stores the difference in a counter.
- The second EEM applet is triggered based on the counter values.
I’m collecting tips like this one in the Embedded Event Manager (EEM) workshop. You can attend an online version of the workshop; we can also organize a dedicated event for your networking team.
Here’s the source code for the first applet (he had to execute CLI show commands to work around the CB-QoS MIB limitations).
Update: workaround for sluggish CB-QoS MIB
More than a year ago, I wrote about the very slow update rate of the variables in the CB-QoS MIB. In August WB found a workaround (do a show policy-map interface before reading the counters) and now Jared has tested it and confirmed that it works. He’s configured a simple EEM applet that executes the show command once per second:
event manager applet UpdateMibTables
event timer watchdog time 1
action 1.0 cli command "enable"
action 2.0 cli command "show policy-map int dialer0"
With this fix, he can use the SNMP variables in other EEM applets to detect VoIP calls within 1-2 seconds.
Don’t forget: numerous EEM topics are described in the Embedded Event Manager (EEM) workshop. You can attend an online version of the workshop; we can also organize a dedicated event for your networking team.
IPv6 CPE router requirements
It’s almost unbelievable: more than 10 years after the IPv6 specs have been completed, someone finally realized it would be a good idea to specify the minimum requirements for a decent IPv6 CPE router. While this document will not solve the lack of low-cost IPv6-ready CPE devices, it’s definitely a step in the right direction, more so as it clearly acknowledges the need for DHCPv6 (some people still believe SLAAC is the solution to every problem ever invented).
Here are a few highlights from the document:
IP over DWDM
A while ago I was pushed (actually it was a kind nudge) into another interesting technology area: optical networks, with emphasis on IP over DWDM. I realized almost immediately that I’d encountered another huge can of worms. A few issues you can stumble across when trying to plug routers or switches directly into DWDM networks are documented in my IP over dense wave division multiplexing (DWDM): Metro and core issues article recently published by SearchTelecom.com.
Cloud computing and public transport
Greg Ferro has republished an older post in which he compares Cloud Computing with public transport (and notes that nothing has changed in more than a year since he wrote the original article). His analogy is more than fitting; a perfect example is Google’s new Google Docs offering, where Stephen Foskett did a nice cost analysis of the unsupported service as compared to supported one.
I’m describing aspects of cloud computing in its various incarnations in my Next-generation IP Services workshop. You can attend an online version of the workshop or we can organize a dedicated event for your team.
Translated into public transport terms: if you want to fly cheap, choose Ryan Air (in Google’s case, you pay 25 cents per gigabyte per year); if you want reasonable support and flexibility, use Lufthansa ($3.50 per gigabyte per year for Google Apps Premier Edition customers or 14 times more than the unsupported capacity).
If you’re unhappy with my choice of airlines, insert your own selection in the above paragraph ;)
NAT-PT is totally broken in late IOS releases
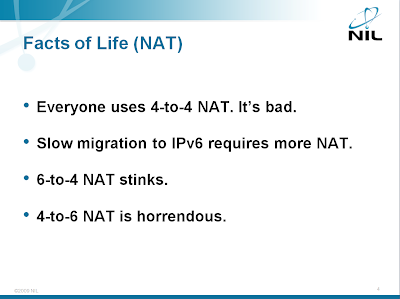
When the current variant of IPv6 was selected 15 years ago, seamless integration with IPv4 was a big deal, resulting in NAT-PT architecture. NAT-PT tried to solve too many problems and (as I pointed out in my IPv6 Deployment workshop), while the 6to4 NAT is manageable, the 4to6 NAT is horrific (NAT64 and DNS64 are more reasonable; more about them in an upcoming post).
NAT between IPv4 and IPv6 hosts is just one of the topics covered in the Enterprise IPv6 Deployment workshop. You can attend an online version of the workshop or we can organize a dedicated event for your team.
To make matters worse, the NAT-PT implemented in Cisco IOS is totally broken due to removal of fast switching support in IOS release 12.4(20)T and numerous other releases. As I wrote a year and a half ago, removing fast switching will bite us eventually … and so it does when you try to use NAT-PT.
Rant: The long-term consequences of book piracy
A few hours after I’ve published my review of the “Cisco routers for the desperate” book someone posted a link to a digital (pirated) copy of the book to my Facebook page, no doubt feeling like a hero fighting for the freedom of information (or some similar nonsense).
I didn’t even try to download the book to see whether it was a leaked copy from the publisher (in which case someone has some serious problems) or a scanned PDF.
Weird GPRS and UMTS latency
Bad designer sent me an interesting comment: 2G and 3G networks have huge latency issues. GPRS is intolerable, UMTS is awful and HSPDA is reasonable but still not what one would hope for.
The latency does not seem to be associated with serialization delay. UMTS gives you reasonable transfer rates and significant latency and GPRS gives you an order of magnitude higher latency than ISDN with comparable transfer rate. If anyone knows enough about the mobile technologies to explain this phenomenon (or at least give me useful pointers) I’d really appreciate your comments.