IPv6 in the Data Center: is Cisco ready?
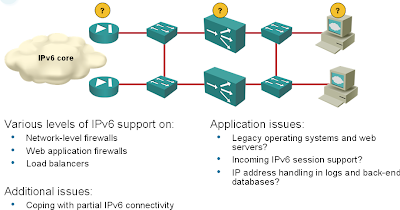
With the recent Cisco’s push into the Data Center environment and all the (not so very unreasonable) fuss around IPv4 address depletion and imminent need for IPv6, I wanted to check whether an all-Cisco shop could do the first step: deploy IPv6 on Internet-facing production servers. If you follow the various design guidelines, your setup will have at least the following elements (and I bet someone from Cisco has already told you that you also need XML firewall, Ironport and WAAS appliance):
Now let’s see how well these boxes support IPv6.
I’m describing the Data Center IPv6 deployment issues in the Enterprise IPv6 Deployment workshop. The diagram above was taken straight from the workshop materials.
Routers and switches (both Catalysts running SXI release and Nexuses running latest NX-OS) support everything you need, including IPv6 layer 3 virtualization (IPv6 in VRF, also known as 6vPE).
I couldn’t find 6vPE support in IOS XE Release 2, but then you’d most likely need it on the core switches, not on the edge routers.
ASA is a bit of a problem – the current software release does not support failover configurations with IPv6. The situation rapidly worsens as you go deeper into the Application Networking Services. I wasn’t able to find any mention of IPv6 in ACE, XML Gateway or WAAS configuration guides. If I’ve missed something, please let me know.
The status of IPv6 support in various Data Center components is summarized in the following table:
| Equipment | Level of IPv6 support |
|---|---|
| Routers | Yes (6vPE on IOS XE might be missing) |
| Firewalls (ASA) | No redundancy (IPv6 failover doesn’t work) |
| Data center switches | Yes (Catalyst and Nexus) |
| Firewall Service Module (FWSM) | Not in transparent mode, on the main CPU (awfully slow) in routed mode. |
| Load balancers (ACE) | No |
| Application-level firewall (XML Gateway) | No |
| WAN optimization (WAAS) | No |
| Ironport | No |

Apparently 8.2(2) will solve some of these issues...
PS. Ivan, why do you say 6VPE is not likely needed on edge routers? The edge is -exactly- where you need it imho.