While according to the GIFEE True Believers™, Docker is dead and Kubernetes rules the world, people who want to have a bit of life might be perfectly happy running “obsolete” stuff like Docker on their laptops or Linux VMs.
If you happen to be one of the latter, you might like the Introduction to Docker webinar I put together a few years ago. It’s now public; you can watch it with an ipSpace.net account.
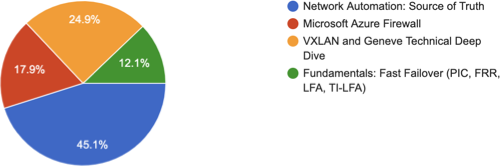
Looking for more binge-watching materials? You’ll find them here.
]]>